-
 軟體損壞資料救援
軟體損壞資料救援
誤分割、誤格式化、誤ghost、駭客攻擊、PQ調整失敗等... -
 硬體損壞資料救援
硬體損壞資料救援
電路板芯片燒壞,不認碟、碟體書寫錯誤等... -
 伺服器資料救援
伺服器資料救援
磁碟陣列RAID0 、RAID1、RAID1+0、NAS、SAN 、JBO -
 筆電資料救援
筆電資料救援
東芝、日立、邁拓、三星、富士通、昆騰、筆記型等... -
 RAID資料救援
RAID資料救援
對RAID0、RAID1、RAID1E、RAID5E、RAID6等救援... -
 硬碟資料救援
硬碟資料救援
IDE、SCSI、S-ATA介面的IBM、易拓,昆騰硬碟,移動硬碟...
OpenBSD DHCPD 服務程序遠程棧溢出漏洞
【綠盟科技授權,賽迪發佈,謝絕任何網站轉載,違者,賽迪網將保留追究其法律責任的權利!】
發佈日期:2007-10-09
更新日期:2007-10-11
受影響系統:
OpenBSD OpenBSD 4.2
OpenBSD OpenBSD 4.1
OpenBSD OpenBSD 4.0
描述:
--------------------------------------------------------------------------------
BUGTRAQ ID: 25984
CVE(CAN) ID: CVE-2007-5365
OpenBSD是一款開放源代碼Unix類操作系統。
OpenBSD系統的DHCP協議實現上存在緩衝區溢出漏洞,遠程攻擊者可能利用此漏洞控制伺服器。
OpenBSD的options.c文件中的cons_options()函數沒有正確地處理DHCP請求。如果遠程攻擊者所發送的DHCP請求中指定最大消息大小小於最小IP MTU(278)的話,就會在OpenBSD中導致dhcpd(8)覆蓋棧緩衝區,執行任意指令。
漏洞存在於負責處理從客戶端所接收到的DHCP選項的函數中。在src/usr.sbin/dhcpd/options.c文件中:
int
cons_options(struct packet *inpacket, struct dhcp_packet *outpacket,
int mms, struct tree_cache **options,
int overload, /* Overload flags that may be set. */
int terminate, int bootpp, u_int8_t *prl, int prl_len)
{
unsigned char priority_list[300];
int priority_len;
unsigned char buffer[4096]; /* Really big buffer... */
int main_buffer_size;
int mainbufix, bufix;
int option_size;
int length;
dhcp.h中定義了DHCP_FIXED_LEN:
if (!mms &&
inpacket &&
inpacket->options[DHO_DHCP_MAX_MESSAGE_SIZE].data &&
(inpacket->options[DHO_DHCP_MAX_MESSAGE_SIZE].len >=
sizeof(u_int16_t)))
mms = getUShort(
inpacket->options[DHO_DHCP_MAX_MESSAGE_SIZE].data);
if (mms)
main_buffer_size = mms - DHCP_FIXED_LEN;
else if (bootpp)
main_buffer_size = 64;
else
main_buffer_size = 576 - DHCP_FIXED_LEN;
if (main_buffer_size > sizeof(buffer))
main_buffer_size = sizeof(buffer);
main_buffer_size是有符型,可被攻擊者控制。只要main_buffer_size是比較小的正整數(<= 4096),執行流就會正常進行:
/* Copy the options into the big buffer... */
option_size = store_options(
buffer,
(main_buffer_size - 7 + ((overload & 1) ? DHCP_FILE_LEN : 0)+
((overload & 2) ? DHCP_SNAME_LEN : 0)),
options, priority_list, priority_len, main_buffer_size,
(main_buffer_size + ((overload & 1) ? DHCP_FILE_LEN : 0)),
terminate);
/* Put the cookie up front... */
memcpy(outpacket->options, DHCP_OPTIONS_COOKIE, 4);
mainbufix = 4;
這裡如果main_buffer_size為比較小的正值的話(<= 7),就會導致store_options迅速退出,執行流會繼續。具體來講,只要客戶端報文中的Maximum Segment Size值(mms)滿足(DHCP_FIXED_LEN < mms < DHCP_FIXED_LEN+4)這個條件,main_buffer_size就會為小於4的正數。
if (option_size <= main_buffer_size - mainbufix) {
memcpy(&outpacket->options[mainbufix],
buffer, option_size);
mainbufix += option_size;
if (mainbufix < main_buffer_size)
outpacket->options[mainbufix++] = DHO_END;
length = DHCP_FIXED_NON_UDP + mainbufix;
} else {
outpacket->options[mainbufix++] = DHO_DHCP_OPTION_OVERLOAD;
outpacket->options[mainbufix++] = 1;
if (option_size >
main_buffer_size - mainbufix + DHCP_FILE_LEN)
outpacket->options[mainbufix++] = 3;
else
outpacket->options[mainbufix++] = 1;
memcpy(&outpacket->options[mainbufix],
buffer, main_buffer_size - mainbufix);
用負數的第三個參數觸發memcpy(3)調用就會導致覆蓋大部分的進程記憶體。
<*來源:Gera Richarte
Nahuel Riva
鏈接:http://www.openbsd.org/errata40.html
http://secunia.com/advisories/27160/
http://www.openbsd.org/cgi-bin/cvsweb/src/usr.sbin/dhcpd/options.c
http://marc.info/?l=bugtraq&m=119212200825215&w=2
http://www.debian.org/security/2007/dsa-1388
*>
建議:
--------------------------------------------------------------------------------
廠商補丁:
Debian
------
Debian已經為此發佈了一個安全公告(DSA-1388-3)以及相應補丁:
DSA-1388-3:New dhcp packages fix arbitrary code execution
鏈接:http://www.debian.org/security/2007/dsa-1388
補丁下載:
Source archives:
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2.dsc
Size/MD5 checksum: 683 0b58f9e8eb121cf97c069580fe7f8d2a
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2.diff.gz
Size/MD5 checksum: 109536 e05751df16af9fef3826de1b13b19694
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5.orig.tar.gz
Size/MD5 checksum: 294909 ab22f363a7aff924e2cc9d1019a21498
alpha architecture (DEC Alpha)
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_alpha.deb
Size/MD5 checksum: 115986 5a3fad1441184f67ebfd259e225b8deb
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_alpha.deb
Size/MD5 checksum: 122958 70cf5573cdb9df0ade56fd58963526f7
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_alpha.deb
Size/MD5 checksum: 81466 59a2774d3cbf426c116cda5b37004b02
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_alpha.udeb
Size/MD5 checksum: 53328 fc6a74bbf4ca3d11266894022967d215
amd64 architecture (AMD x86_64 (AMD64))
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_amd64.deb
Size/MD5 checksum: 115646 5fb5be9e0df58591e2f09984b107b6ff
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_amd64.deb
Size/MD5 checksum: 76622 699bdea9722e30a17d893a5fdfc59b3c
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_amd64.deb
Size/MD5 checksum: 109336 aca4a6dfbe89e12da8b5f57031c6749a
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_amd64.udeb
Size/MD5 checksum: 46762 b7ab045411264337a230c0e0547e976c
arm architecture (ARM)
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_arm.deb
Size/MD5 checksum: 114446 e706691fe1b1da3e48556f3f3a2759dc
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_arm.udeb
Size/MD5 checksum: 44804 a7de3008bff776bc41f57939d6baef0c
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_arm.deb
Size/MD5 checksum: 74574 c357f51c69cacd0c5e7f746735b050ee
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_arm.deb
Size/MD5 checksum: 107660 c0426fafa16454f4f3613b669be104b3
hppa architecture (HP PA RISC)
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_hppa.deb
Size/MD5 checksum: 115078 77698ad1416708c1bba42286717a6a38
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_hppa.deb
Size/MD5 checksum: 109288 ba099d48d08c7b63f17c901505069a93
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_hppa.deb
Size/MD5 checksum: 77218 631787f11690111a20ca8e06da223955
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_hppa.udeb
Size/MD5 checksum: 46534 e4563d516472ae7b00640c4faf63a69b
i386 architecture (Intel ia32)
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_i386.udeb
Size/MD5 checksum: 40922 439ee79ca28a824a3bd702e6d2a4782a
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_i386.deb
Size/MD5 checksum: 72582 ad568458d95419eae37cbc05f7df99e0
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_i386.deb
Size/MD5 checksum: 111342 02946828ab4646c8c9d40abbb9323f10
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_i386.deb
Size/MD5 checksum: 103662 5309abf9853a42438f3b25557e2ea72a
ia64 architecture (Intel ia64)
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_ia64.deb
Size/MD5 checksum: 135918 1130320929adbd7b5f6bbbdbe7ea8cf4
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_ia64.deb
Size/MD5 checksum: 142464 88880a0d9631738e8d50d88725405f2a
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_ia64.udeb
Size/MD5 checksum: 72360 4c6b9e4ed5a2b908818f2bdc047302f1
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_ia64.deb
Size/MD5 checksum: 92714 6b45e56a178149eb662b3ace829f4d1a
mips architecture (MIPS (Big Endian))
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_mips.deb
Size/MD5 checksum: 112086 f3eefe99badef8981c197191cfa7ad39
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_mips.deb
Size/MD5 checksum: 118180 bc2b4fcd3d3a7df0ece598e4a0c72ea4
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_mips.udeb
Size/MD5 checksum: 49302 0a4a229e0e066b8d9fecc75125385899
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_mips.deb
Size/MD5 checksum: 78638 a588b355c89a2f5bbd893aaf938740c8
mipsel architecture (MIPS (Little Endian))
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_mipsel.deb
Size/MD5 checksum: 117674 a39185fab632a03793efe3396311f350
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_mipsel.udeb
Size/MD5 checksum: 48770 42c311ba6c2052abdddf6c2e6b7aa16a
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_mipsel.deb
Size/MD5 checksum: 111554 86440305699bfed9cd6cd0721b5c032c
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_mipsel.deb
Size/MD5 checksum: 78272 95b3aff8d41ea810ee4d4b1bb75c9eed
powerpc architecture (PowerPC)
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_powerpc.deb
Size/MD5 checksum: 74674 f3377454115baffb9450fb0a0bb51d0f
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_powerpc.deb
Size/MD5 checksum: 105862 4b75aabdc533969677988dbc4bd8e59e
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_powerpc.udeb
Size/MD5 checksum: 43066 2edba1128225890a6792f2eecee00058
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_powerpc.deb
Size/MD5 checksum: 112228 a60c4734706546a47127c11765f1d9bf
s390 architecture (IBM S/390)
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_s390.udeb
Size/MD5 checksum: 53540 8a063f95dd410c93e6b5fe10e091fdc2
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_s390.deb
Size/MD5 checksum: 121934 d5ae65fdd1254df11d692051753efcc8
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_s390.deb
Size/MD5 checksum: 116260 29bf7983a2226601124ee0da48072aa2
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_s390.deb
Size/MD5 checksum: 80346 fe7c1452e141fc20d16653b857d6ec69
sparc architecture (Sun SPARC/UltraSPARC)
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-relay_2.0pl5-19.5etch2_sparc.deb
Size/MD5 checksum: 75060 e8e5a86e2e608771e36755b0f443df83
http://security.debian.org/pool/updates/main/d/dhcp/dhcp_2.0pl5-19.5etch2_sparc.deb
Size/MD5 checksum: 112946 cd73de6703a63dc321cf788bab64d52d
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client_2.0pl5-19.5etch2_sparc.deb
Size/MD5 checksum: 106534 c777f24901a5bdb9db29c3a82da401d8
http://security.debian.org/pool/updates/main/d/dhcp/dhcp-client-udeb_2.0pl5-19.5etch2_sparc.udeb
Size/MD5 checksum: 43554 516673e6c0d38126058807dbbdf81fe7
補丁安裝方法:
1. 手工安裝補丁包:
首先,使用下面的命令來下載補丁軟體:
# wget url (url是補丁下載鏈接地址)
然後,使用下面的命令來安裝補丁:
# dpkg -i file.deb (file是相應的補丁名)
2. 使用apt-get自動安裝補丁包:
首先,使用下面的命令更新內部資料庫:
# apt-get update
然後,使用下面的命令安裝更新軟體包:
# apt-get upgrade
OpenBSD
-------
目前廠商已經發佈了升級補丁以修復這個安全問題,請到廠商的主頁下載:
ftp://ftp.openbsd.org/pub/OpenBSD/patches/4.0/common/016_dhcpd.patch
ftp://ftp.openbsd.org/pub/OpenBSD/patches/4.1/common/010_dhcpd.patch
ftp://ftp.openbsd.org/pub/OpenBSD/patches/4.2/common/001_dhcpd.patch
(
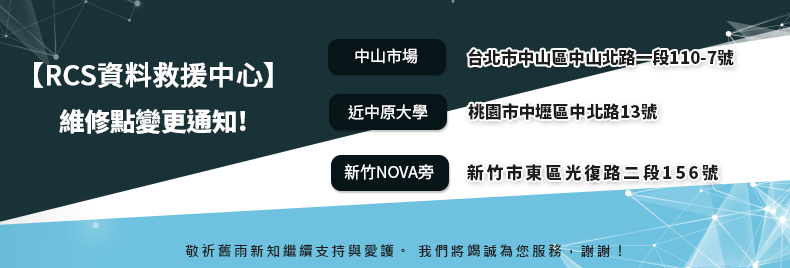
台北資料救援:115台北市南港區三重路19-11號E棟(南港軟體園區)
新竹資料救援:300新竹市東區光復路二段156號
新竹科學園區資料救援:新竹科學工業園區新安路5號4樓 (鴻海大樓裡面)
台南資料救援:700台南市中西區北門路一段57號 TEL:06-505-0005

線上客服
@hd119