-
 軟體損壞資料救援
軟體損壞資料救援
誤分割、誤格式化、誤ghost、駭客攻擊、PQ調整失敗等... -
 硬體損壞資料救援
硬體損壞資料救援
電路板芯片燒壞,不認碟、碟體書寫錯誤等... -
 伺服器資料救援
伺服器資料救援
磁碟陣列RAID0 、RAID1、RAID1+0、NAS、SAN 、JBO -
 筆電資料救援
筆電資料救援
東芝、日立、邁拓、三星、富士通、昆騰、筆記型等... -
 RAID資料救援
RAID資料救援
對RAID0、RAID1、RAID1E、RAID5E、RAID6等救援... -
 硬碟資料救援
硬碟資料救援
IDE、SCSI、S-ATA介面的IBM、易拓,昆騰硬碟,移動硬碟...
Cisco 操作系統IOS存在DLSw拒絕服務漏洞
【綠盟科技授權,賽迪發佈,謝絕任何網站轉載,違者,賽迪網將保留追究其法律責任的權利!】
【賽迪網-IT技術報道】Cisco IOS在處理UDP和IP 91協議報文時存在多個漏洞,這些漏洞不影響TCP報文處理,成功攻擊可能導致系統重啟或設備記憶體洩露,造成拒絕服務的情況。
發佈日期:2008-03-26
更新日期:2008-04-08
受影響系統:
Cisco IOS 12.4
Cisco IOS 12.3
Cisco IOS 12.2
Cisco IOS 12.1
Cisco IOS 12.0
描述:
--------------------------------------------------------------------------------
BUGTRAQ ID: 28465
CVE(CAN) ID: CVE-2008-1152
Cisco IOS是思科網絡設備中所使用的互聯網操作系統。
資料-鏈路交換(DLSw)允許通過IP網絡傳輸IBM系統網絡架構(SNA)和網絡基本輸入/輸出系統(NetBIOS)通訊。Cisco的DLSw實現還使用UDP 2067端口和IP 91協 議進行快速順序傳輸(FST)。
Cisco IOS在處理UDP和IP 91協議報文時存在多個漏洞,這些漏洞不影響TCP報文處理,成功攻擊可能導致系統重啟或設備記憶體洩露,造成拒絕服務的情況。
<*來源:Cisco安全公告
鏈接:http://secunia.com/advisories/29507/
http://www.cisco.com/warp/public/707/cisco-sa-20080326-dlsw.shtml
http://www.us-cert.gov/cas/techalerts/TA08-087B.html
*>
建議:
--------------------------------------------------------------------------------
臨時解決方法:
* 如下配置iACL
|
* 如下配置控制面整形(CoPP)
|
請注意在Cisco IOS 12.2S和12.0S系列中policy-map句法有所不同:
|
廠商補丁:
Cisco
-----
Cisco已經為此發佈了一個安全公告(cisco-sa-20080326-dlsw)以及相應補丁:
cisco-sa-20080326-dlsw:Multiple DLSw Denial of Service Vulnerabilities in Cisco IOS
鏈接:http://www.cisco.com/warp/public/707/cisco-sa-20080326-dlsw.shtml
(
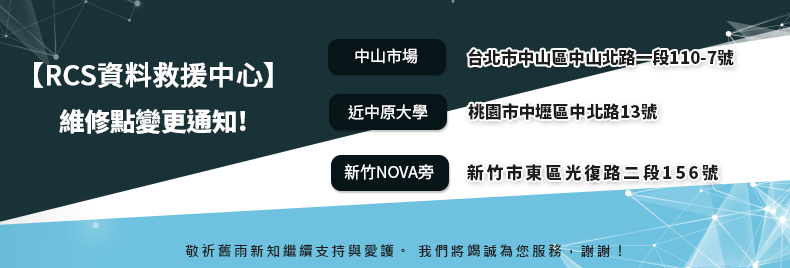
台北資料救援:115台北市南港區三重路19-11號E棟(南港軟體園區)
新竹資料救援:300新竹市東區光復路二段156號
新竹科學園區資料救援:新竹科學工業園區新安路5號4樓 (鴻海大樓裡面)
台南資料救援:700台南市中西區北門路一段57號 TEL:06-505-0005

線上客服
@hd119